Administrators occasionally need to check complicated settings and security structures for users. Sometimes the easiest and most reliable way to do so is to simply log in as that user. Pyramid provides an innovative solution by allowing an administrator to simply log in as a specific user and see exactly what they see.
Server-based software with governance allows different functionality to users dependent on the roles and security structures that are applied to them. For example, role-specific security might hide financial measures from clerical roles, or customer names may be hidden from unauthorized users to comply with Payment Card Industry (PCI) standards. This requires users to log in and test before deploying tenant-, role-, or user-based content.
Pyramid’s impersonate feature allows administrator users to “Log in as a User” to emulate non-administrator users, fully experiencing all content and menu options as if they were the user. This enables comprehensive troubleshooting of all user and role-based logic, without requiring user testing (which might involve ghost logins or other workarounds) before releasing a feature. Advanced logic that uses user-based functions and security can also be tested by administrators.
Example
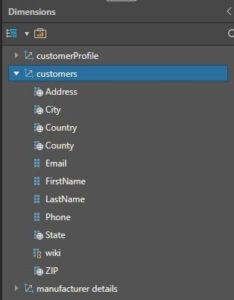
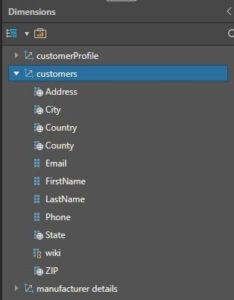
The administrator views the customer dimensions available from the Discover module, where all personal attributes including name, address, email, and phone are available.
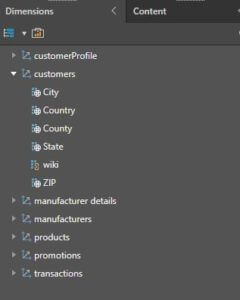
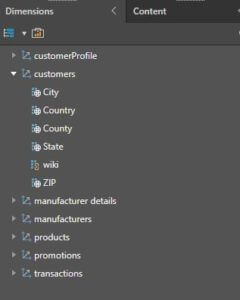
The administrator sets up role-based security for the ‘Analysts’ role by disabling the Customer name, address, email, and phone attributes. All users logging in under the Analysts role will not be able to see any of these details.

The administrator then clicks on the Impersonate button for a user categorized under the “Analysts” role.

Upon opening a Discover report, none of the personal details are available for display.
Summary
Pyramid administrators can “impersonate” any user by logging in as that user without their credentials, enabling quick and easy testing of user-related issues before releasing features into a test or production environment.